Gift card fraud
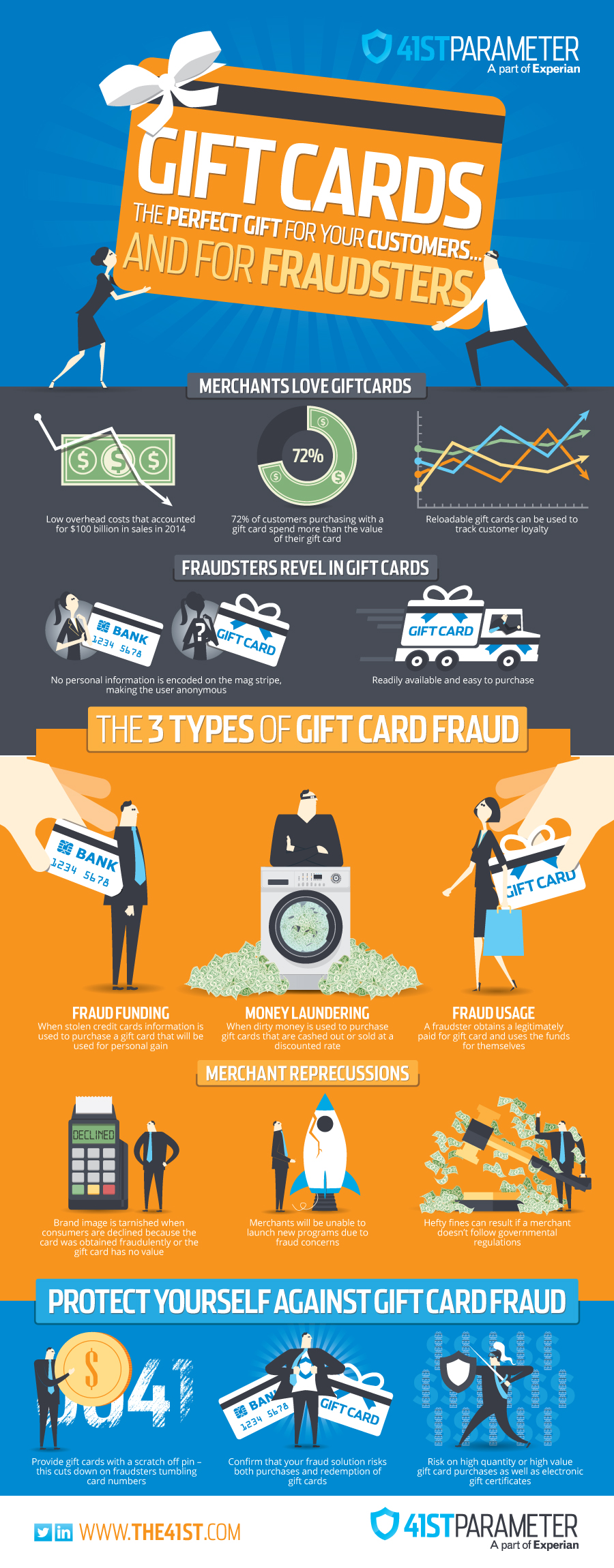 Gift cards have risen in popularity over the last few years— National Retail Federation anticipated more than $31B in gift card sales during the 2014 holiday season alone. Gift cards are the most requested gift item, and they have been for eight years in a row. Total gift card sales for 2014 were anticipated to top $100 Billion.
Gift cards have risen in popularity over the last few years— National Retail Federation anticipated more than $31B in gift card sales during the 2014 holiday season alone. Gift cards are the most requested gift item, and they have been for eight years in a row. Total gift card sales for 2014 were anticipated to top $100 Billion.
Gift cards are a practical gift–the purchaser can let the recipient pick exactly what they want, eliminating the worry of picking something that doesn’t fit right, that is a duplicate, or something that the recipient just might not want. They are also incredibly convenient, quick, and easy to purchase. The stigma behind gift cards is starting to fade, and it no longer seems as though they are an impersonal gifting option.
Additionally, the type of gift cards available has expanded greatly in the last few years. If you are of the procrastinating nature, there are eGift Cards or eCertificates, which can be emailed in a matter of minutes to the recipient. If you are truly unsure what to purchase altogether, you can give an open-loop card, which are usually branded by Visa, MasterCard, and American Express, and can be used anywhere their logo appears.
It also seems like a quick win for merchants to carry gift cards. The overhead cost to store them is extremely low because a small box of gift cards takes up very little space. When customers come in to redeem their GC, they usually spend more than the original value of the card itself, thus allowing for additional revenue capture.
Something else that merchants have started doing in this big data world we live in is tying gift cards to consumer loyalty programs. Reloadable cards are now linked to a specific customer, who can also tie their credit card to the account, which is automatically charged once their account is below a pre-defined threshold. These new consumer loyalty accounts can be used to track spending history, tailor offers to the specific customer, and continue to expand on the immersive brand experience.
Recently, a certain Mexican-themed fast food establishment launched their new mobile app; in the app, you could pre-order food, send and redeem eGCs, and find the nearest location. I don’t even eat at this establishment, but the innovation of their app was so enticing that I installed it the morning it came out, purchased an eGC for my husband, and pre-ordered breakfast. It was extremely easy and convenient, and I got a free taco! Now they have my soul. Okay, maybe not my soul, but they have my credit card data, purchasing preferences, device information, and location, which is almost the same thing at this point. After the experience I found myself asking why other merchants haven’t already done this or why it hasn’t taken off yet. This is a great example of how gift cards and emerging technology are being used as a marketing tool to entice consumers to build up a customer base.
In the rare instance that a gift recipient does not actually find value in their gift card (the horror!) there’s a multitude of options for trading them in or redeeming for cash. Some well-known websites for trade-in are Giftcard Granny, Card Hub, and raise.com; it’s also incredibly common to find discounted GCs for sale on eBay, Craigslist, and Facebook groups. A couple familiar names that have recently entered into the mix are Wal-Mart and CoinStar. You can now exchange your physical gift card for cash at a specific CoinStar machines, and if you don’t feel like leaving your home, you can exchange your card online with Wal-Mart, and they will provide you with a Wal-Mart gift card that can be redeemed online or in stores. It’s such common practice that you can find articles on this topic on local, national, and 24-hour news websites.
This tremendous revenue booster does not come free of risk, however. We know that fraudsters are clever and opportunistic. They will penetrate every weakness possible and take advantage of programs that are being used to enhance the consumer experience. But are they really stealing all these gift cards for personal gain and taking all of their friends out to their favorite local coffee shop for free drinks? Stay tuned for the second part of this blog that talks more about the fraud risks associated with gift cards and what you can do to mitigate them.
Please note: *The use of GC/eGC is used interchangeably.


