Tag: synthetic ID

Last month, Kenneth Blanco, Director of the Financial Crimes Enforcement Network, warned that cybercriminals are stealing data from fintech platforms to create synthetic identities and commit fraud. These actions, in turn, are alleged to be responsible for exploiting fintech platforms’ integration with other financial institutions, putting banks and consumers at risk. According to Blanco, “by using stolen data to create fraudulent accounts on fintech platforms, cybercriminals can exploit the platforms’ integration with various financial services to initiate seemingly legitimate financial activity while creating a degree of separation from traditional fraud detection efforts.” Fintech executives were quick to respond, and while agreeing that synthetic IDs are a problem, they pushed back on the notion that cybercriminals specifically target fintech platforms. Innovation and technology have indeed opened new doors of possibility for financial institutions, however, the question remains as to whether it has also created an opportunity for criminals to implement more sophisticated fraud strategies. Currently, there appears to be little evidence pointing to an acute vulnerability of fintech firms, but one thing can be said for certain: synthetic ID fraud is the fastest-growing financial crime in the United States. Perhaps, in part, because it can be difficult to detect. Synthetic ID is a type of fraud carried out by criminals that have created fictitious identities. Truly savvy fraudsters can make these identities nearly indistinguishable from real ones. According to Kathleen Peters, Experian’s SVP, Head of Fraud and Identity, it typically takes fraudsters 12 to 18 months to create and nurture a synthetic identity before it’s ready to “bust out” – the act of building a credit history with the intent of maxing out all available credit and eventually disappearing. These types of fraud attacks are concerning to any company’s bottom line. Experian’s 2019 Global Fraud and Identity Report further details the financial impact of fraud, noting that 55% of businesses globally reported an increase in fraud-related losses over the past 12 months. Given the significant risk factor, organizations across the board need to make meaningful investments in fraud prevention strategies. In many circumstances, the pace of fraud is so fast that by the time organizations implement solutions, the shelf life may already be old. To stay ahead of fraudsters, companies must be proactive about future-proofing their fraud strategies and toolkits. And the advantage that many fintech companies have is their aptitude for being nimble and propensity for early adoption. Experian can help too. Our Synthetic Fraud Risk Level Indicator helps both fintechs and traditional financial institutions in identifying applicants likely to be associated with a synthetic identity based on a complex set of relationships and account conditions over time. This indicator is now available in our credit report, allowing organizations to reduce exposure to identity fraud through early detection. To learn more about Experian’s Synthetic Fraud Risk Level Indicator click here, or visit experian.com/fintech.

It’s Halloween time – time for trick or treating, costume parties and monsters lurking in the background. But this year, the monsters aren’t just in the background. They’re in your portfolio. This year, “Frankenstein” has another meaning. Much more ominous than the neighbor kid in the costume. “Frankenstein IDs” refer to synthetic identities — a type of fraud carried out by criminals that have created fictitious identities. Just as Dr. Frankenstein’s monster was stitched together from parts, synthetic IDs are stitched together pieces of mismatched identities — some fake, some real, some even deceased. It typically takes fraudsters 12 to 18 months to create and nurture a synthetic identity before it’s ready to "bust out" – the act of building a credit history with the intent of maxing out all available credit and eventually disappearing. That means fraudsters are investing money and time to build numerous tradelines, ensure these "fake" identities are in good credit standing, and ultimately steal the largest amount of money possible. “Wait Master, it might be dangerous . . . you go, first.” — Igor Synthetic identities are a notable challenge for many financial institutions and retail organizations. According to the recently released Federal Reserve Board White Paper, synthetic identity fraud accounts for roughly 20% of all credit losses, and cost U.S. businesses roughly $6 billion in 2016 with an estimated 41% growth over 2 years. 85-95% of applicants identified as potential synthetic are not even flagged by traditional fraud models. The Social Security Administration recently announced plans for the electronic Consent Based Social Security Number Verification service – pilot program scheduled for June 2020. This service is designed to bring efficiency to the process for verifying Social Security numbers directly with the government agency. Once available, this verification could be an important tool in the fight against the elusive “Frankenstein” identity monster. But with the Social Security Administration's pilot program not scheduled for launch until the middle of next year, how can financial institutions and other organizations bridge the gap and adequately prepare for a potential uptick in synthetic identity fraud attacks? It comes down to a multilayered approach that relies on advanced data, analytics, and technology — and focuses on identity. Any significant progress in making synthetic identities easier to detect could cost fraudsters significant time and money. Far too many financial institutions and other organizations depend solely on basic demographic information and snapshots in time to confirm the legitimacy of an identity. These organizations need to think beyond those capabilities. The real value of data in many cases lies between the data points. We have seen this with synthetic identity — where a seemingly legitimate identity only shows risk when we can analyze its connections and relationships to other individuals and characteristics. In addition to our High Risk Fraud Score, we now have a Synthetic Fraud Risk Level Indicator available on credit profiles. These advanced detection capabilities are delivered via the simplicity of a straightforward indicator returned on the credit profile which lenders can use to trigger additional identity verification processes. While there are programs and initiatives in the works to help financial institutions and other organizations combat synthetic identity fraud, it's important to keep in mind there's no silver bullet, or stake to the heart, to completely keep these Frankenstein IDs out. Oh, and don’t forget… “It’s pronounced ‘Fronkensteen.’ ” — Dr. Frankenstein

Experian is excited to have been chosen as one of the first data and analytics companies that will enable access to Social Security Administration (SSA) data for the purposes of verifying identity against the Federal Agency’s records. The agency’s involvement in the wake of Congressional interest and successful legislation will create a seismic shift in the landscape of identity verification. Ultimately, the ability to leverage SSA data will reduce the impact of identity fraud and synthetic identity and put real dollars back into the pockets of people and businesses that absorb the costs of fraud today. As this era of government and private sector collaboration begins, many of our clients and partners are breathing a sigh of relief. We see this in a common question our customers ask every day, “Do I still need an analytical solution for synthetic ID now that eCBSV is on the horizon?” The common assumption is that help is on the way and this long tempest of rising losses and identity uncertainty is about to leave us. Or is it? We don’t believe it’s the end of the synthetic ID storm. This is the eye. Rather than basking in the calm light of this moment, we should be thinking ahead and assessing our vulnerabilities because the second half of this storm will be worse than the first. Consider this: The people who develop and exploit synthetic IDs are playing a long game. It takes time, research, planning and careful execution to create an identity that facilitates fraud. The bigger the investment, the bigger the spoils will be. Synthetic ID are being used to purchase luxury automobiles. They’re passing lender marketing criteria and being offered credit. The criminals have made their investment, and it’s unlikely they will walk away from it. So, what does SSA’s pending involvement mean to them? How will they prepare? These aren’t hard questions. They’ll do what you would do in the eye of a storm — maximize the value of the preparations that are in place. Gather what you can quickly and brace yourself for the uncertainty that’s coming. In short, there’s a rush to monetize synthetic IDs on the horizon, and this is no time to declare ourselves safe. It’s doubtful that the eCBSV process will be the silver bullet that ends synthetic ID fraud — and certainly not on day one. It’s more likely that the physical demands of the data exchange, volume constraints, response times and the actionability of the results will take time to optimize. In the meantime, the criminals aren’t going to sit by and watch as their schemes unravel and lose value. We should take some comfort that we’ve made it through the first half of the storm, but recognize and prepare for what still needs to be faced.

Experian has been named one of the 10 participants, and only credit bureau, in the initial rollout of the SSA's new eCBSV service.
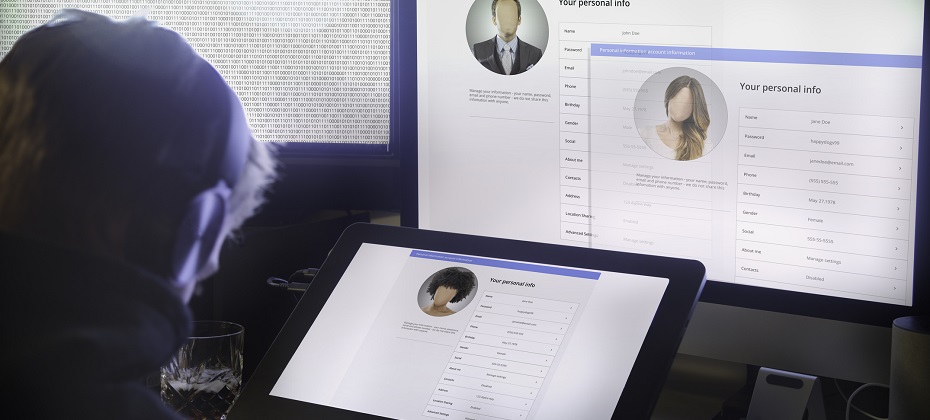
Friend or foe? Sophisticated criminals put a great deal of effort into creating convincing, verifiable personas (AKA synthetic identities). Once the fictional customer has embedded itself in your business, everything from the acquisition of financial instruments to healthcare benefits, utility services, and tax filings and refunds become vulnerable to synthetic identity fraud. Information attached to synthetic IDs can run several levels deep and be so complete that it includes public record data, credit information, documentary evidence and social media profiles that may even contain photo sets and historical details intended to deceive—all complicating your efforts to identify these fake customers before you do business with them. See real-world examples of how synthetic identity fraud is souring various markets – from auto and healthcare to financial services and public sector – in our tip sheet, Four common synthetic scenarios. Stopping synthetic ID fraud — at the door and thereafter. There are efforts underway in the market to collectively improve your ability to identify, shut down and prevent synthetic identities from entering your portfolio. This overall trend is great news for the future, but there are also near-term solutions you can apply to protect your business starting now. While it’s important to identify synthetic identities when they knock on your door, it’s just as important to conduct regular portfolio checkups to prevent negative impacts to your collections efforts. Every circumstance has its own unique parameters, but the overarching steps necessary to mitigate fraud from synthetic IDs remain the same: Identify current and near-term exposure using targeted segmentation analysis. Apply technology that alerts you when identity data doesn’t add up. Differentiate fraudulent identities from those simply based on bad data. Review front- and back-end screening procedures until they satisfy best practices. Achieve a “single view of the customer” for all account holders across access channels—online, mobile, call center and face-to-face. The right tools for the job. In addition to the steps mentioned above, stopping these fake customers from entering and then stealing from your organization isn’t easy—but with the right tools and strategies, it is possible. Here are a few of our top recommendations: Forensics Isolate and segment identities based on signals received during early account pathing, from both individuals and their device. For example, even sophisticated fraud networks can’t mimic natural per-device user interaction because these organizations work with hundreds or thousands of synthetic identities using just a few devices. It’s highly unlikely that multiple geographically separate account holders would share the same physical device. High-risk fraud scores Not all synthetic identity fraud manifests the same way. Using sophisticated logic and unique combinations of data, a high-risk fraud score looks at a consumer’s credit behavior and credit relationships over time to uncover previously undetectable risk. These scores are especially successful in detecting identities that are products of synthetic identity farms. And by targeting a specific data set and relationships, you can maintain a frictionless customer experience and reduce false positives. Analytics Use a solution that develops models of bad applicant behavior, then compares and scores your portfolio against these models. There isn’t a single rule for detecting fraudulent identities, but you can develop an informed set of rules and targeted models with the right service partner. Cross-referencing models designed to isolate high-risk identity theft cases, first-party or true-name fraud schemes, and synthetic identities can be accomplished in a decisioning strategy or via a custom model that incorporates the aggregate scores and attributes holistically. Synthetic identity detection rules These specialized rules consist of numerous conditions that evaluate a broad selection of consumer behaviors. When they occur in specific combinations, these behaviors indicate synthetic identity fraud. This broad-based approach provides a comprehensive evaluation of an identity to more effectively determine if it’s fabricated. It also helps reduce the incidence of inaccurately associating a real identity with a fictitious one, providing a better customer experience. Work streams Address synthetic identities confidently by applying analytics to work streams throughout the customer life cycle: Credit risk assessment Know Your Customer/Customer Identification Program checks Risk-based identity proofing and authentication Existing account management Manual reviews, investigations and charge-offs/collections activities Learn more about these tools and others that can help you mitigate synthetic identities in our white paper, Synthetic identities: getting real with customers. If your organization is like most, detecting SIDs hasn't been your top priority. So, there's no time to waste in preventing them from entering your portfolio. Criminals are highly motivated to innovate their approaches as rapidly as possible, and it’s important to implement a solution that addresses the continued rise of synthetic IDs from multiple engagement points. With the right set of analytics and decisioning tools, you can reduce exposure to fraud and losses stemming from synthetic identity attacks from the beginning and across the customer life cycle. We can help you detect and mitigate these fake customers before they become delinquent. Learn more

Synthetic identities come from accounts held not by actual individuals, but by fabricated identities created to perpetrate fraud. It often starts with stealing a child’s Social Security number (SSN) and then blending fictitious and factual data, such as a name, a mailing address and a telephone number. What’s interesting is the increase in consumer awareness about synthetic identities. Previously, synthetic identity was a lender concern, often showing itself in delinquent accounts since the individual was fabricated. Consumers are becoming aware of synthetic ID fraud because of who the victims are — children. Based on findings from a recent Experian survey, the average age of child victims is only 12 years old. Children are attractive victims since fraud that uses their personal identifying information can go for years before being detected. I recently was interviewed by Forbes about the increase of synthetic identities being used to open auto loans and how your child’s SSN could be used to get a phony auto loan. The article provides a good overview of this growing concern for parents and lenders. A recent Javelin study found that more than 1 million children were victims of fraud. Most upsetting is that children are often betrayed by people close to them -- while only 7 percent of adults are victimized by someone they know, 60 percent of victims under 18 know the fraudster. Unfortunately, when families are in a tight spot financially they often resort to using their child’s SSN to create a clean credit record. Fraud is an issue we all must deal with — lenders, consumers and even minors — and the best course of action is to protect ourselves and our organizations.

Although it’s hard to imagine, some synthetic identities are being used for purposes other than fraud. Here are 3 types of common synthetic identities and why they’re created: Bad — To circumvent lag times and delays in establishing a legitimate identity and data footprint. Worse — To “repair” credit, hoping to start again with a higher credit rating under a new, assumed identity. Worst — To commit fraud by opening various accounts with no intention of paying those debts or service fees. While all these synthetic identity types are detrimental to the ecosystem shared by consumers, institutions and service providers, they should be separated by type — guiding appropriate treatment. Learn more in our new white paper produced with Whitepages Pro, Fighting synthetic identity theft: getting beyond Social Security numbers. Download now>

While it’s important to recognize synthetic identities when they knock on your door, it’s just as important to conduct regular portfolio checkups. Every circumstance has unique parameters, but the overarching steps necessary to mitigate fraud from synthetic IDs remain the same: Identify current and near-term exposure using targeted segmentation analysis. Apply technology that alerts you when identity data doesn’t add up. Differentiate fraudulent identities from those simply based on bad data. Review front- and back-end screening procedures until they satisfy best practices. Achieve a “single customer view” for all account holders across access channels — online, mobile, call center and face-to-face. With the right set of analytics and decisioning tools, you can reduce exposure to fraud and losses stemming from synthetic identity attacks at the beginning and across the Customer Life Cycle. Learn more

Traditional verification and validation parameters alone are not enough to stop identity fraud. Fortunately, there are many emerging trends and best practices for modern fraud and identity strategies: Applying right-sized fraud and identity proofing solutions to reduce user friction and manage fraud risk appropriately. Maintaining a universal user view by employing diverse breadth and depth of data assets and applied analytics. Expanding the user view through a blended ecosystem by collaborating with vendors, peer agencies, and partners in identity and fraud management. The future of identity proofing is more than just verifying individual identities. Check out our tip sheet linked below for more strategies. Modernize your fraud and identity strategies>

Experian on the State of Identity podcast In today’s environment, any conversation on the identity management industry needs to include some mention of synthetic identity risk. The fact is, it’s top of mind for almost everyone. Institutions are trying to scope their risk level and identify losses, while service providers are innovating ways to solve the problem. Even consumers are starting to understand the term, albeit via a local newscast designed to scare the heck out of them. With all this in mind, I was very happy to be invited to speak with Cameron D’Ambrosi at One World Identity (OWI) on the State of Identity podcast, focusing on synthetic identity fraud. Our discussion focused on some of the unique findings and recommended best practices highlighted in our recently published white paper on the subject, Synthetic identities: getting real with customers. Additionally, we discussed how a lack of agreement on the definition and size of the synthetic identity problem further complicates the issue. This all stems from inconsistent loss reporting, a lack of confirmable victims and an absence of an exact definition of a synthetic identity to begin with. Discussions must continue to better align us all. I certainly appreciate that OWI dedicated the podcast to this subject. And I hope listeners take away a few helpful points that can assist them in their organization’s efforts to better identify synthetic identities, reduce financial losses and minimize reputation risks.

The data to create synthetic identities is available. And the marketplace to exchange and monetize that data is expanding rapidly. The fact that hundreds of millions of names, addresses, dates of birth, and Social Security numbers (SSNs) have been breached in the last year alone, provides an easy path for criminals to surgically target new combinations of data. Armed with an understanding of the actual associations of these personally identifiable information (PII) elements, fraudsters can better navigate the path to perpetrate identity theft, identity manipulation, or synthetic identity fraud schemes on a grand scale. Using information such as birth dates and addresses in combination with Social Security numbers, criminals can target new combinations of data to yield better results with lower risk of detection. Some examples of this would be: identity theft, existing account takeovers, or the deconstruction and reconstruction of those PII elements to better create effective synthetic identities. Experian has continued to evolve and innovate against fraud risks and attacks with an understanding of attack rates, vectors, and the shifting landscape in data availability and security. In doing so, we’ve historically operated under the assumption that all PII is already compromised in some way or is easily done so. Because of this, we employ a layered approach, providing a more holistic view of an identity and the devices that are used over time by that identity. Relying solely on PII to validate and verify an identity is simply unwise and ineffective in this era of data compromise. We strive to continuously cultivate the broadest and most in-depth set of traditional, innovative and alternative data assets available. To do this, we must enable the integration of diverse identity attributes and intelligence to balance risk, while maintaining a positive customer experience. It’s been quite some time since the use of basic PII verification alone has been predictive of identity risk or confidence. Instead, validation and verification is founded in the ongoing definition and association of identities, the devices commonly used by those individuals, and the historical trends in their behavior. Download our newest White Paper, Synthetic Identities: Getting real with customers, for an in-depth Experian perspective on this increasingly significant fraud risk.

Synthetic identity fraud is on the rise across financial services, ecommerce, public sector, health and utilities markets. The long-term impact of synthetic identity remains to be seen and will hinge largely upon forthcoming efforts across the identity ecosystem made up of service providers, institutions and agencies, data aggregators and consumers themselves. Making measurement more challenging is the fact that much of the assumed and confirmed losses are associated with credit risk and charge offs, and lack of common and consistent definitions and confirmation criteria. Here are some estimates on the scope of the problem: Losses due to synthetic identity fraud are projected to reach more than $800 million in 2017.* Average loss per account is more than $10,000.* U.S. synthetic credit card fraud is estimated to reach $1.257 billion in 2020.* As with most fraud, there is no miracle cure. But there are best practices, and topping that list is addressing both front- and back-end controls within your organization. Synthetic identity fraud webinar> *Aite Research Group

Mitigating synthetic identities Synthetic identity fraud is an epidemic that does more than negatively affect portfolio performance. It can hurt your reputation as a trusted organization. Here is our suggested 4-pronged approach that will help you mitigate this type of fraud: Identify how much you could lose or are losing today to synthetic fraud. Review and analyze your identity screening operational processes and procedures. Incorporate data, analytics and cutting-edge tools to enable fraud detection through consumer authentication. Analyze your portfolio data quality as reported to credit reporting agencies. Reduce synthetic identity fraud losses through a multi-layer methodology design that combats both the rise in synthetic identity creation and use in fraud schemes. Mitigating synthetic identity fraud>

The creation of synthetic identities (synthetic id) relies upon an ecosystem of institutions, data aggregators, credit reporting agencies and consumers. All of which are exploited by an online and mobile-driven market, along with an increase in data breaches and dark web sharing. It’s a real and growing problem that’s impacting all markets. With significant focus on new customer acquisition and particular attention being paid to underbanked, emerging, and new-to-country consumers, this poses a large threat to your onboarding and customer management policies, in addition to overall profitability. Synthetic identity fraud is an epidemic that does more than negatively affect portfolio performance. It can hurt your reputation as a trusted organization and expose institutions, like yours, as paths of lesser resistance for fraudsters to use in the creation and farming of synthetic identities. Here is a suggested four-pronged approach to mitigate this type of fraud: The first step is knowing your risk exposure to synthetic identity fraud. Identify how much you could lose or are losing today using a targeted segmentation analysis to examine portfolios or customer populations. Next, review your front- and back-end identity screening operational processes and procedures and analyze that information to ensure you have industry best practices, procedures and verification tools deployed. Then incorporate data, analytics and some of the industry’s cutting edge tools. This enables you to perform targeted consumer authentication and identify opportunities to better capture the majority of fraud and operational waste. Lastly, ensure your organization is part of the solution – not the problem. Analyze your portfolio data quality as reported to credit reporting agencies and then minimize your exposure to negative compliance audit results and reputational risk. Our fraud and identity management consultants can help you reduce synthetic identity fraud losses through a multilayer methodology design that combats the rise in synthetic identity creation and use in fraud schemes.

Part four in our series on Insights from Vision 2016 fraud and identity track It was a true honor to present alongside Experian fraud consultant Chris Danese and Barbara Simcox of Turnkey Risk Solutions in the synthetic and first-party fraud session at Vision 2016. Chris and Barbara, two individuals who have been fighting fraud for more than 25 years, kicked off the session with their definition of first-party versus third-party fraud trends and shared an actual case study of a first-party fraud scheme. The combination of the qualitative case study overlaid with quantitative data mining and link analysis debunked many myths surrounding the identification of first-party fraud and emphasized best practices for confidently differentiating first-party, first-pay-default and synthetic fraud schemes. Following these two passionate fraud fighters was a bit intimidating, but I was excited to discuss the different attributes included in first-party fraud models and how they can be impacted by the types of data going into the specific model. There were two big “takeaways” from this session for me and many others in the room. First, it is essential to use the correct analytical tools to find and manage true first-party fraud risk successfully. Using a credit score to identify true fraud risk categorically underperforms. BustOut ScoreSM or other fraud risk scores have a much higher ability to assess true fraud risk. Second is the need to for a uniform first-party fraud bust-out definition so information can be better shared. By the end of the session, I was struck by how much diversity there is among institutions and their approach to combating fraud. From capturing losses to working cases, the approaches were as unique as the individuals in attendance This session was both educational and inspirational. I am optimistic about the future and look forward to seeing how our clients continue to fight first-party fraud.