Tag: fraud
In an attempt to stay ahead of fraud, systems have become more complex, more expensive and even more difficult to manage, leading to more friction for customers. How extensive is this impact? 30% of online customers are interrupted to catch one fraudulent attempt One in 10 new applicants may be an imposter using breached data $40 billion of legitimate customer sales are declined annually Businesses must continue their efforts to protect all parties’ interests if they are to thrive in this new world of rapid technological growth. >> Infographic: Global fraud trends

We are excited to announce that Experian Fraud and Identity Solutions is presenting at FinovateFall 2016! Finovate conferences showcase cutting-edge banking and financial technology in a unique demo-only format. Held twice a year, the conferences bring together the leaders from top financial institutions, fintech companies, investors from around the globe, and fintech media to share and promote the most innovative financial technology solutions. "Experian’s Fraud and Identity Solutions is a leader in customer-centric identity and fraud solutions, providing fraud management solutions to some of the world’s largest brands in financial services, insurance, and retail," said Adam Fingersh, general manager and senior vice president of Fraud and Identity Solutions in North America. "We will introduce our Fraud and Identity Solutions and promote our newly released CrossCore platform. CrossCore puts more control in the hands of fraud teams to adapt and deploy strategies that keep up with the pace of fraud while reducing burdens on IT and data science teams." Fingersh and John Sarreal, senior director of Fraud and Identity product management at Experian, are presenting the 7-minute demo focusing on the key CrossCore capabilities, and how CrossCore manages fraud and identity services through its flexible API; open, plug-and-play platform; and powerful workflow and strategy design capabilities. In Forrester’s 2016 “Vendor Landscape: Mobile Fraud Management”, Experian Fraud and Identity Solutions was cited as having the most capabilities and one of the highest estimated revenues in total fraud management in the market, between $200 million and $250 million. Join us for the event on September 8-9 in New York. Experian also has an exclusive 20% off discount code (Experian20FF16) to get even more savings! For more information on the event or to view videos of previous demos, please visit finovate.com.

New industry report highlights the convergence of business growth and fraud prevention strategies Experian has published its first annual global fraud report covering the convergence of growth strategies and fraud prevention. The report, Global Business Trends: Protecting Growth Ambitions Against Rising Fraud Threats, is designed as a guide for senior executives and fraud prevention professionals, offering new insights on how the alignment of strategies for business growth and fraud prevention can help a business grow revenues while managing risks in an increasingly virtual world. The report identifies five trends that businesses should assess and take action on to mitigate fraud and improve the customer experience in today's fast-paced, consumer-centric environment: Applying right-sized fraud solutions to reduce unnecessary customer disruption: It's time to move on from a one-size-fits-all approach that creates more customer friction than necessary. Instead, companies should apply fraud solutions that reflect the value and level of confidence needed for each transaction. This means right-sizing your fraud solutions to align with true fraud rates and commercial strategy. Having a universal view of the consumer is the core of modern fraud mitigation and marketing: Achieving a universal profile of consumer behavior — beyond the traditional 360-degree view — requires access to a combination of identity data, device intelligence, online behavior, biometrics, historical transactions and more, for consumer interactions not only with you, but across other businesses and industries as well. Companies that translate this knowledge and use it to identify consumers can distinguish a fraudster from a real customer more easily, building trust along the way. Expanding your view through a blended ecosystem: In addition to using your own first-party data sources, companies need to participate in a blended ecosystem, working across businesses and even industries. Fraudsters have access to more data than ever before, including data traditionally used to verify identities, and they use that data to create an entire digital profile. Therefore, you can no longer get to the digital interaction data you need by managing the process in a siloed manner. Achieving an expansive view of the universal consumer requires multiple data sources working together. Achieving agility and scale using service-based models: Today, more and more companies are choosing subscription-based systems rather than building in-house or implementing on-premise solutions. Continuous upgrades and the access to new risk logic that come with subscription models provide more agility and faster response to emerging threats, no matter how fast your volume grows or what products, channels or geographies you pursue. Future-proofing fraud solution choices: Companies need access to a wide variety of traditional and emerging technologies and information sources to fill in knowledge gaps and blind spots where fraudsters try to hide. The ability to modify strategies quickly and catch fraud faster while improving the customer experience is a critical aspect of fraud prevention moving forward. Bringing together these key trends, the report provides business leaders with the insight they need to fight fraud using the same consumer-focused approach currently being used to attract new customers and grow revenue. "There is a persistent mindset that fraud loss is just the cost of doing business," said Steve Platt, global EVP, Fraud and Identity, Experian. "But as fraudsters evolve, those losses are climbing, and the status quo is no longer effective or acceptable. We all need to be as forward-looking in fighting fraud as we are in business operations and marketing, and a real understanding of consumers is critical for success. We're talking about the convergence of business growth and fraud prevention, and we're pleased to provide the first report in the marketplace covering this topic." Download the full report here. The report also features an interactive Fraud Prevention Benchmark tool that companies can use to explore how these trends impact their business and how the performance of their approach measures up against industry practices. The report is relevant to functions spanning the enterprise, including C-suite executives such as chief marketing officers (CMOs), chief risk officers (CROs) and chief data officers (CDOs). The report focuses on business processes where fraud infiltrates, including new account opening, account access, money movement transactions, and emerging trends combating fraud, such as advanced fraud analytics. In each area, the report details how multiple business functions can apply responses to create business growth. Steve Platt added: "We hear from our clients that they are most successful when CMOs along with CDOs and CROs all work together to understand the customer and develop fraud management solutions that create a better overall experience." Experian was recently cited in Forrester's 2016 Vendor Landscape: Mobile Fraud Management Solutions1 report and listed as having nine out of a possible 10 capabilities needed to combat mobile fraud. Experian was also identified as one of three leading players in the fraud detection and prevention space in a new study from Juniper Research.2 Experian applied best practices to create a global report on providing fraud management solutions that allow companies to maximize profitability while providing secure, hassle-free customer interactions. Learn more about Experian’s Fraud and Identity business. 1Vendor Landscape: Mobile Fraud Management Solutions, Forrester Research, Inc., June 2016. 2Online Payment Fraud: Key Vertical Strategies & Management 2016–2020, Juniper Research, June 2016.
Many fraud and compliance teams are struggling to keep pace with new business dynamics. Here are several of the many mobile device trends affecting business today: 35% year-over-year growth in mobile commerce from 2014-2015 Value of mobile payment transactions is forecasted to reach more than $27 billion in 2016 45% of smartphone owners use a mobile device to make a purchase every month This rapid growth only reinforces the need for aggressive fraud prevention strategies and the adoption of new technologies to prepare for the latest emerging cybersecurity threats. >> Forrester's 2016 Vendor Landscape: Mobile Fraud Management Solutions Report

Is the speed of fraud threatening your business? Like many other fraud and compliance teams, your teams may be struggling to keep up with new business dynamics. The following trends are changing the way consumers do business with you: 35 percent year-over-year growth in mobile commerce More than $27 billion forecasted value of mobile payment transactions in 2016 45 percent of smartphone owners using a mobile device to make a purchase every month More than 1 billion mobile phone owners will use their devices for banking purposes by the end of 2015 In an attempt to stay ahead of fraud, systems have become more complex, more expensive and even more difficult to manage, leading to more friction for your customers. How extensive is this impact? 30 percent of online customers are interrupted to catch one fraudulent attempt One in 10 new applicants may be an imposter using breached data $40 billion of legitimate customer sales are declined annually because of tight rules, processes, etc. This rapid growth only reinforces the need for aggressive fraud prevention strategies and adoption of new technologies to prepare for the latest emerging cybersecurity threats. Businesses must continue their efforts to protect all parties’ interests. Fraudsters have what they need to be flexible and quick. So why shouldn’t businesses? Introducing CrossCore™, the first smart plug-and-play platform for fraud and identity services. CrossCore uses a single access point to integrate technology from different providers to address different dangers. When all your fraud and identity solutions work together through a single application program interface, you reduce friction and false positives — meaning more growth for your business. View our recent infographic on global fraud trends

Every day, millions of new things get connected online, such as toasters, heart monitors and cars. Many of these things have weak security controls that create vulnerabilities in critical private networks. As more products get connected, the casual mindset about the security risks inherent in the Internet of Things must begin to change. Here are 12 tips to help safeguard your systems from the Internet of Things. >> Securing the Internet of Things

Experian cited in Mobile Fraud Management Solutions report from Forrester as having the most capabilities and one of the highest estimated revenues in total fraud management

Part 3 in our series on Insights from the Vision 2016 fraud and identity track Our Vision 2016 fraud track session titled “Deployment Made Easy — solving new fraud problems by Adapting Legacy Solutions” offered insights into the future of analytics and the mechanisms for delivering them. The session included two case studies, the first of which highlighted a recently completed project in which an Experian client struggling with rising application fraud losses had to find a way to deploy advanced analytics without any IT resources. To assist the customer, data passing through an existing customer interface was reformatted and redirected to our Precise ID® platform. Upon arrival in Precise ID, a custom-built fraud scoring model was invoked. The results were then translated back into the format used by the legacy interface so that they could be ingested by the customer’s systems. This case study illustrates the key value proposition of Experian’s new CrossCoreTM fraud and identity platform. CrossCore features a similar “translation layer” for inquiries coming into Experian’s fraud and identity tools that will allow customers to define fraud-screening workflows that call a variety of services. The IT burden for connecting the inquiry to various Experian and non-Experian services will fall on Experian — sparing the customer from the challenge of financing and prioritizing IT resources. Similarly, the output from CrossCore will provide a ready-to-consume response that integrates directly with our customers’ host systems. The audience showed keen interest in the “here and now” illustration of what CrossCore will enable. Our second case study was provided by Eric Heikkila at Amazon Web Services™ and focused on the future of analytics. For an audience accustomed to the constraints of developing advanced analytics in a rigid data-structure, Amazon’s description of a “data lake” was a fascinating picture of what’s possible. The data lake offers the simultaneous ability to accommodate existing structured customer data along with new unstructured data in an infinitely scalable data set. Equally important is the data lake’s ability to accommodate an unlimited array of data mining and analytical tools. Amazon’s message was clear and simple — the fraud industry’s trepidation around the use of big data is misplaced. The fear of making the wrong choice of data storage and analytical tools is unnecessary. To illustrate this point, Eric shared an Amazon Web Services case study that used FINRA (Financial Industry Regulatory Authority). FINRA is responsible for overseeing U.S. securities markets to ensure that rules are followed and integrity is maintained. Amid a bewildering set of ever-changing regulations and peak volumes of 35 trillion per day — yes, trillion — Amazon’s data lake supports both the scale and analytical demands of a complex industry. As the delivery and access to fraud products is made easy by CrossCore, the data and analytics will expand through the use of services like Amazon’s data lake. As the participants will agree, the future of fraud technology is closer than you think!

Part 2 in our series on Insights from the Vision 2016 fraud and identity track With the growing number of data breach incidents taking place the stolen data from those attacks is being used to carry out social engineering attacks used to commit call center fraud. A recent study stated that global call center fraud has increased more than 45% in the last three years as fraudsters use social engineering to steal data and turn profits. The same report found that criminals might make up to 5 calls to a center, pretending to be the victim, before completing a fraudulent transaction. The importance of strong call center authentication procedures is greater than ever. At the 35th annual Vision Conference, Bobbie Paul from Experian’s Global Consulting Practice, Stefan Schubert from JPMorgan Chase and I led a session about call center authentication. After introductions and a discussion about existing call center identity authentication techniques, Stefan took the podium and provided an excellent overview of how his company approaches call center authentication. He made an interesting point — despite introducing friction into his process, he was not of the opinion that knowledge-based authentication (KBA) was going away any time soon because of how deeply it is embedded into their processes and its applicability to most consumers. He also called out the importance of reviewing KBA configurations regularly to adjust which questions are being asked and the positive implication to deterring fraudsters. Bobbie followed Stefan to discuss emerging call center authentication technologies, including a new take on an old tool — document imaging. She also discussed the notion of phone printing, which does not specifically evaluate the voice on the phone, but looks at the characteristics of the call itself, including the type of phone being used and the environment from which the call is being made. One of the highlights of the session was the interaction with the audience — including a demonstration of how, with a little distraction, it was easy to walk away with an audience member’s phone, how a fraudster could access and compromise a phone and how a gummy bear could be used to defeat fingerprint biometrics. What I, and many others, took away from this is that even with newer fraud detection tools available, incorporating tried-and-true methods like KBA is still an important step into a holistic fraud detection strategy.
Industry’s first smart plug-and-play fraud platform allows companies to connect their own solutions, Experian products and third-party vendors in one place to better protect their customers from fraud threats Experian unveiled the fraud and identity industry’s first open platform designed to catch fraud faster, improve compliance and enhance the customer experience. Experian’s CrossCore™ gives companies an easier way to connect any new or existing tools and systems in one place, whether they are Experian, internal or third-party partner solutions. This “plug-and-play” capability allows companies to rapidly adapt to changing conditions and risks. “Our clients have expressed frustration over the lack of a truly holistic industry solution that delivers the level of confidence and control they need without requiring a massive multiyear project to replace everything they have,” said Steve Platt, global executive vice president, Fraud and Identity, Experian. “New fraud threats, updates to regulatory requirements and customer expectations for a hassle-free experience are making it challenging for fraud and compliance teams to keep up. CrossCore will give them the flexibility they need to balance customer protection with customer experience.” The CrossCore open platform enables organizations to manage services through a common access point that supports a layered approach to managing risks across providers. CrossCore includes powerful workflow and strategy design capabilities that allow fraud and compliance teams to create and adapt strategies based on evolving threats and business needs. This helps them to respond more quickly and reduces the burden on IT. Fraud and compliance teams must constantly respond to new fraud threats and changing regulatory requirements by implementing new tools on top of existing solutions. “A layered approach is imperative, because fraudsters can break through each layer individually, but they will face greater barriers with each additional layer imposed,” said Avivah Litan, vice president and distinguished analyst, Security and Privacy, of Gartner.[1] Over time, as layers have been added and fortified, systems have become increasingly complex, expensive to integrate and difficult to manage, often increasing customer friction. A key feature of the CrossCore fraud platform is the ease of integration with third-party partner solutions. At launch, CrossCore will support fraud and identity services provided by third-party partners, including Acxiom® (Identity Solutions), TeleSign and many others already integrated with Experian solutions, with more being added to the platform. Previously, integrating third-party solutions required tremendous time and effort, which often challenged in-house teams to execute in a timely, efficient manner. Through CrossCore, the responsibility of integrating additional tools and systems moves away from those teams to the platform itself, enabling clients to select best-in-class solutions from multiple providers without creating a strain on resources. Al Pascual, senior vice president, research director and head of fraud & security for Javelin, said, “There are so many great niche solutions to work with, and new ones come out almost every day. To really have a world-class approach, the client has to put all those little things together, because there never will be one vendor who does it all. The market challenge is about how to make it faster and easier to bring things together to enable a more dynamic and fluid approach to managing risk.” CrossCore features Common access through a flexible API connects disparate systems to improve risk controls while reducing integration cost and complexity An open approach enables clients to connect and optimize a portfolio of best-in-class solutions across Experian, third-party services and existing systems Powerful strategy design and workflow decisioning functions enable fraud and compliance teams to apply services in any combination to get the level of confidence required A modern Software as a Service (SaaS) architecture provides scalability and the ability to make strategy changes dynamically with no down time Experian, which offers fraud and identity services in more than 44 countries, developed CrossCore to address the widespread market need consistently expressed by its clients for a faster, easier way to get more out of their existing systems and add new tools to improve their customers’ experience while minimizing risk. Companies can begin accessing CrossCore immediately, with the ability to turn on Experian services through a single integration, connect their own fraud and identity capabilities with a common API and turn on new services as they are added. The initial release includes key Experian products: FraudNet for Account Opening; Hunter®, for application fraud detection; Prove-ID, for international identity verification; and Precise ID®, for U.S. identity verification, including knowledge-based authentication. (KBA). Third-party fraud and identity service providers can engage with CrossCore to connect their services. “Now, companies can implement a new approach to managing fraud and identity services — one that will give them greater control over their risk exposure and enable them to provide a safer and more enjoyable experience for their customers,” added Platt. Learn more about CrossCore at https://www.experian.com/crosscore [1]Gartner, Identity Proofing Revisited as Data Confidentiality Dies, Avivah Litan, Dec. 12, 2013; last reviewed on April 28, 2015

Last week we had the pleasure of joining more than 400 clients at the 35th annual Vision Conference — connecting business leaders to ideas and solutions. Over the next few weeks, we’ll be sharing some insights from our fraud and identity dedicated session track. I had the pleasure of presenting alongside the U.S. Secret Service, and we had a packed session to discuss the Dark Web — what it is, how it’s accessed, how criminals are exploiting it to commit fraud and the human impact of the massive global cybercrime problem. According to McAfee®, cybercrime represents a $500 billion cost to the global economy — and that’s projected to rise to $600 billion this year, outpacing any other form of crime. With the Internet economy generating between $2 trillion and $3 trillion annually, that means cybercrime is extracting roughly 15 to 20 percent of the entire value created by the Internet. This is a massive problem, and it’s not going away. Unfortunately, there are countless tools and services to commit fraud available on the Web, providing attackers with the cloak of anonymity they need to compromise accounts, mimic legitimate users and submit fraudulent transactions. Device intelligence helps unmask these activities. It is a critical component to defend against the threat, and it provides insight into every interaction throughout a typical customer journey (from account setup to login and account maintenance to transactions). Without this visibility into users’ historical behavior and typical population patterns, organizations often have limited options to target attackers and identify anomalous behaviors. This is key to a successful cybercrime detection and mitigation strategy. Another important point in the session regarded recent law enforcement and private industry successes in identifying, tracking, apprehending and prosecuting online attackers. We thankfully have made significant strides in this area, as evidenced by the work of the Secret Service and other law enforcement organizations, but the collaboration must continue — and intensify. As mentioned in a CNBC story published on the same day as our presentation, the Dark Web is an increasingly mainstream source for everything from financial crime to drug trade and human trafficking. Unfortunately, most businesses are in the dark about the growing criminal underground, but Experian can help. With proper fraud expertise and innovative tools to defend against these ever-evolving threats, organizations can uncloak the attackers and safeguard the business.

False declines are often unwarranted and occur due to lack of customer information Have you ever been shopping online, excited to get your hands on the latest tech gadget, only to be hit with the all-too-common disappointment of a credit card decline? Whom did you blame? The merchant? The issuer? The card associations? The answer is probably all of the above. False declines like the situation described above provoke an onslaught of consumer emotions ranging from shock and dismay to frustration and anger. Of course, consumers aren’t the only ones negatively impacted by false declines. Many times card issuers lose their coveted “top of wallet” position and/or retailers lose revenue when customers abandon the purchase altogether. False declines are unpleasant for everyone, yet consumers struggle with this problem every day — and fraud controls are only getting tighter. How does the industry mutually resolve this growing issue? The first step is to understand why it occurs. Most false declines happen when the merchant or issuer mistakenly declines a legitimate transaction due to perceived high risk. This misperception is usually the result of the merchant or issuer not having enough information to verify the authenticity of the cardholder confidently. For example, the consumer may be a first-time customer or the purchase may be a departure from the card holder’s normal pattern of transaction activity. Research shows that lack of a holistic view and no cross-industry transaction visibility result in approximately $40 billion of e-commerce declines annually. Think about this for a minute — $40 billion in preventable lost revenue due to lack of information. Merchants’ customer information is often limited to their first-hand information and experience with consumers. To solve this growing problem, Experian® developed TrustInsight™, a real-time engine to establish trusted online relationships over time among consumers, merchants and issuers. It works by anonymously leveraging transactional information that merchants and financial institutions already have about consumers to create a crowd-sourced TrustScore™. This score allows first-time online customers to get a VIP experience rather than a brand-damaging decline. Another common challenge for merchants is measuring the scope of the false declines problem. Proactively contacting consumers, directly capturing feedback and quickly verifying transaction details to recoup potential lost sales are best practices, but merchants are often in the dark as to how many good customers are being turned away. The solution — often involving substantial operational expense — is to hold higher-risk orders for manual review rather than outright declining them. With average industry review rates nearing 30 percent of all online orders (according to the latest CyberSource Annual Fraud Benchmark Report: A Balancing Act), this growing level of review is not sustainable. This is where industry collaboration via TrustInsight™ offers such compelling value. TrustInsight can reduce the review population significantly by leveraging consumers’ transactions across the network to establish trust between individuals and their devices to automate more approvals. Thankfully, the industry is taking note. There is a groundswell of focus on the issue of false declines and their impact on good customers. Traditional, operations-heavy approaches are no longer sufficient. A trust-based industry-consortium approach is essential to enhance visibility, recognize consumers and their devices holistically, and ensure that consumers are impacted only when a real threat is present.

This article first appeared in Baseline Magazine Since it is possible for cyber-criminals to create a synthetic person, businesses must be able to differentiate between synthetic and true-party identities. Children often make up imaginary friends and have a way of making them come to life. They may come over to play, go on vacation with you and have sleepover parties. As a parent, you know they don’t really exist, but you play along anyway. Think of synthetic identities like imaginary friends. Unfortunately, some criminals create imaginary identities for nefarious reasons, so the innocence associated with imaginary friends is quickly lost. Fraudsters combine and manipulate real consumer data with fictitious demographic information to create a “new” or “synthetic” individual. Once the synthetic person is “born,” fraudsters create a financial life and social history that mirrors true-party behaviors. The similarities in financial activities make it difficult to detect good from bad and real from synthetic. There really is no difference in the world of automated transaction processing between you and a synthetic identity. Often the synthetic “person” is viewed as a thin or shallow file consumer— perhaps a millennial. I have a hard time remembering all of my own passwords, so how do organized “synthetic schemes” keep all the information usable and together across hundreds of accounts? Our data scientists have found that information is often shared from identity to identity and account to account. For instance, perhaps synthetic criminals are using the same or similar passwords or email addresses across products and accounts in your portfolio. Or, perhaps physical address and phone records have cross-functional similarities. The algorithms and sciences are much more complex, but this simplifies how we are able to link data, analytics, strategies and scores. Identifying the Business Impact of Synthetic-Identity Fraud Most industry professionals look at synthetic-identity fraud as a relatively new fraud threat. The real risk runs much deeper in an organization than just operational expense and fraud loss dollars. Does your fraud strategy include looking at all types of risk, compliance reporting, and how processes affect the customer experience? To identify the overall impact synthetic identities can have on your institution, you should start asking: Are you truly complying with "Know Your Customer" (KYC) regulations when a synthetic account exists in your active portfolio? Does your written "Customer Identification Program" (CIP) include or exclude synthetic identities? Should you be reporting this suspicious activity to the compliance officer (or department) and submitting a suspicious activity report (SAR)? Should you charge off synthetic accounts as credit or fraud losses? Which department should be the owner of suspected synthetic accounts: Credit Risk, Collections or Fraud? Do you have run any anti-money laundering (AML) risk when participating in money movements and transfers? Depending on your answers to the above questions, you may be incurring potential risks in the policies and procedures of synthetic identity treatment, operational readiness and training practices. Since it is possible to create a synthetic person, businesses must be able to differentiate between synthetic and true-party identities, just as parents need to differentiate between their child's real and imaginary friends.

Device emulators — wolves in sheep’s clothing Despite all the fraud prevention systems and resources in the public and private sectors, online fraud continues to grow at an alarming rate, offering a low-risk, high-reward proposition for fraudsters. Unfortunately, the Web houses a number of easily accessible tools that criminals can use to perpetrate fraud and avoid detection. The device emulator is one of these tools. Simply put, a device emulator is one device that pretends to be another. What began as innovative technology to enable easy site testing for Web developers quickly evolved into a universally available tool that attackers can exploit to wreak havoc across all industry verticals. While it’s not new technology, there has been a significant increase in its use by criminals to deceive simple device identification and automated risk-management solutions to carry out fraudulent activities. Suspected device emulation (or spoofing) traffic historically has been difficult to identify because fraud solutions rely heavily on reputation databases or negative lists. Detecting and defeating these criminals in sheep’s clothing is possible, however. Leveraging Experian’s collective fraud intelligence and data modeling expertise, our fraud research team has isolated several device attributes that can identify the presence of an emulator being used to submit multiple transactions. Thanks to these latest FraudNet rule sets, financial institutions, ecommerce merchants, airlines, insurers and government entities alike now can uncloak and protect against many of these cybercriminals. Unfortunately, device emulators are just one of many tools available to criminals on the Dark Web. Join me at Vision 2016, where U.S. Secret Service and I will share more tales from the Dark Web. We will explore the scale of the global cybercrime problem, walk through the anatomy of a typical hack, explain how hackers exploit browser plug-ins, and describe how enhanced device intelligence and visibility across all channels can stop fraudsters in their tracks. Listen to Mike Gross as he shares a short overview of his Vision 2016 breakout session in this short video. Don’t miss this innovative Vision 2016 session! See you there.
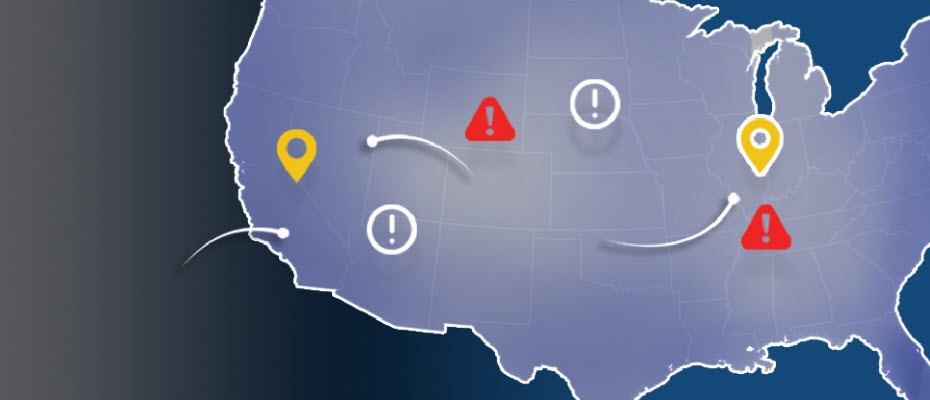
Top states for billing and shipping e-commerce fraud With more than 13 million fraud victims in 2015, assessing where fraud occurs is an important layer of verification for e-commerce. Experian® analyzed millions of e-commerce transactions from 2015 to identify fraud attack rates across the United States. With the switch to chip-enabled credit card transactions and possible growth of card-not-present fraud, online businesses should utilize advanced fraud solutions to monitor their riskiest locations and prevent losses. >> View the Experian map to see 2015 e-commerce attack rates for all states