Fraud & Identity Management
Experian analyzed millions of e-commerce transactions from the first six months of 2016 to identify the latest fraud attack rates across the United States for both shipping and billing locations. As we approach the one-year anniversary of the EMV liability shift, the 2016 e-commerce fraud attack rates look to be at least 15 percent higher than last year’s total. Experian analyzed millions of e-commerce transactions from the first six months of 2016 to identify the latest fraud attack rates across the United States for both shipping and billing locations. Billing fraud rates are associated with the address of the purchaser. Shipping fraud rates are associated with the address where purchased goods are sent. As we approach the one-year anniversary of the EMV liability shift, the 2016 e-commerce fraud attack rates look to be at least 15 percent higher than last year’s total. E-commerce fraud is often an indicator that other fraud activities have already happened, whether a credit card has been stolen, identity fraud has occurred, or personal credentials have been compromised.

Historically, the introduction of EMV chip technology has resulted in a significant drop in card-present fraud, but a spike in card-not-present (CNP) fraud. CNP fraud accounts for 60% to 70% of all card fraud in many countries and is increasing. Merchants and card issuers in the United States likely will see a rise in CNP fraud as EMV migration occurs — although it may be more gradual as issuers and merchants upgrade to chip-based cards. As fraud continues to evolve, so too should your fraud-prevention strategies. Make a commitment to stay abreast of the latest fraud trends and implement sophisticated, cross-channel fraud-prevention strategies. >>Protecting Growth Ambitions Against Rising Fraud Threats

Unfortunately, identity theft can happen to anyone and has far-reaching consequences for its victims. According to the US Department of Justice (DOJ)’s most recent study, 17.6 million people in the US experience some form of identity theft each year. This includes activities such as fraudulent credit card transactions or personal information being used to open unauthorized accounts. The most obvious consequence that identity theft victims encounter is financial loss, which comes in two forms: direct and indirect. Direct financial loss refers to the amount of money stolen or misused by the identity theft offender. Indirect financial loss includes any outside costs associated with identity theft, like legal fees or overdraft charges. The DOJ’s study found that victims experienced a combined average loss of $1,343. In total, identity theft victims lost a whopping $15.4 billion in 2014. Beyond money lost, identity theft can negatively impact credit scores. While credit card companies detect a majority of credit card fraud cases, the rest can go undetected for extended periods of time. A criminal’s delinquent payments, cash loans, or even foreclosures slowly manifest into weakened credit scores. Victims often only discover the problem when they are denied for a loan or credit card application. Last year, Experian found that these types of fraud take the longest time to resolve. Identity theft doesn’t just impact victims financially; it also often takes a significant emotional toll. A survey from the Identity Theft Research Center found that 69 percent felt fear for their personal financial security, and 65 percent felt rage or anger. And, almost 40 percent reported some sleep disruption. These feelings increased over time when victims were unable to settle the issue on their own, according to the report, which can result in problem as work or school, and add stress to relationships with friends and family. Thankfully, consumers are getting smarter about the best ways to protect their information, like using monitoring services or following security best practices. How are you protecting yourself against identity theft? Learn more about our Identity Protection Services
Did you know that identities can shift (for better or worse) in just 30 days? To succeed in today’s multichannel, mobile environment, businesses must have a broader, more dynamic identity management strategy that includes: Identity proofing: Point-in-time verification (e.g., account opening) Authentication: Ongoing verification (e.g., account login) Identity management: Continual monitoring throughout the Customer Life Cycle Minimize your identity fraud risk, increase customer engagement and provide a satisfying customer experience by shifting to a strategy focused on identity relationship management. >>The three pillars of identity relationship management
Experian has been selected as one of the leading players in the fraud detection and prevention space in Juniper Research’s Online Payment Fraud strategies report.

Experian defines how businesses should approach Identity Relationship Management for identity and devices to enable better fraud protection through our latest perspective paper, The 3 Pillars of Identity Relationship Management: How organizations can reduce risk and increase engagement.

Fraudsters invited into bank branches The days of sending an invitation in the mail have for the most part gone by the wayside. Aside from special invitations for weddings and milestone anniversaries, electronic and email invitations have become the norm. However, one major party planner has refused to change practices — banks inviting fraudsters into their banking centers. As a fraud consultant I have the privilege of meeting many banking professionals, and I hear the same issues and struggles over and over again. It’s clear that the rapid increase of fraudulent account-opening applications are top of mind to many. What the executives making policy don’t realize is they’re facing fraud because they’re literally inviting the fraudsters into their branches. Think I’m exaggerating? Let me explain. I often encounter bank policymakers who explain their practice of directing a suspicious person into a banking center. Yes, many banks still direct applicants who cannot be properly verified over the phone or online into their banking center to show proof of identity. Directing or inviting criminals into your bank instead of trying to keep them out is an outdated, high-risk practice — what good can possibly come of it? The argument I typically hear from non-fraud banking professionals: “The bad guys know that if they come into the bank we will have them on film.” Other arguments include that the bad guys are not typically bold enough to actually come into the banking center or that their physical security guards monitor high-traffic banking centers. But often that is where bank policies and employee training ends. Based on my years of experience dealing with banks of all sizes, from the top three global card issuers to small regional banks, let me poke a few holes in the theory that it is a good deterrent to invite perpetrators into your banking center. Let’s role-play how my conversation goes: Me: “When an underwriter with limited fraud training making the decision to direct a suspicious applicant into a banking center, what is the policy criteria to do so?” Bank policymaker: (typical response) “What do you mean?” Me: “What high-risk authentication was used by the underwriter to make the decision to extend an invitation to a high-risk applicant to come into the banking center? If the applicant failed your high-risk authentication questions and you were not able to properly identify them, what authentication tools do the branch managers have that the underwriters do not?” Bank: “Nothing, but they can usually tell when someone is nervous or seems suspicious.” Me: “Then what training do they receive to identify suspicious behaviors?” (You guessed it …) Bank: “None.” (I then switch to the importance of customer experience.) Me: “How do you notify the banking center in advance that the suspicious applicant was invited to come in to provide additional verification?” Bank: “We do not have a policy to notify the banking center in advance.” Me: “What is considered acceptable documentation? And are banking center employees trained on how to review utility statements, state ID cards, drivers’ licenses or other accepted media?“ Bank: “We do not have a list of acceptable documentation that can be used for verification; it is up to the discretion of the banking center representative.” Me: “How do you ensure the physical safety of your employees and customers when you knowingly invite fraudsters and criminals into your banking center? How do you turn down or ask the suspicious person to leave because they do not have sufficient documentation to move forward with the original application for credit? If a suspicious person provides your employee with a possible stolen identification card, is that employee expected to keep it and notify police or return it to the applicant? Are employees expected to make a photocopy of the documentation provided?” The response that I usually receive is, “I am not really sure.” I hope by now you are seeing the risk of these types of outdated practices on suspicious credit applications. The fact is that technology has allowed criminals to make fairly convincing identification at a very low cost. If employees in banking centers are not equipped, properly trained, and well-documented procedures do not exist in your fraud program — perhaps it’s time to reconsider the practice or seek the advice of industry experts. I have spent two decades trying to keep bad guys out of banks, but I can’t help but wonder — why do some still send open invitations to criminals to come visit their bank? If you are not yet ready to stop this type of bad behavior, at the very least you must develop comprehensive end-to-end policies to properly handle such events. This fraud prevention tactic to invite perpetrators into banks was adopted long before the age of real-time decisions, robust fraud scores, big data, decision analytics, knowledge-based authentication, one-time passcodes, mobile banking and biometrics. The world we bank in has changed dramatically in the past five years; customers expect more and tolerate less. If a seamless customer experience and reducing account-opening and first-party fraud are part of your strategic plan, then it is time to consider Experian fraud solutions and consulting.

Experian’s annual global fraud report reveals trends that can help organizations mitigate fraud and improve the customer experience: Apply the right-sized fraud solutions to reduce unnecessary customer disruption Ensure you have a universal consumer view Select fraud solutions that are future-proof As fraudsters evolve, losses are climbing and the status quo is no longer effective. Organizations should be as forward-looking in fighting fraud as they are in business operations and marketing. >> Global Business Trends: Protecting Growth Ambitions Against Rising Fraud Threats
In an attempt to stay ahead of fraud, systems have become more complex, more expensive and even more difficult to manage, leading to more friction for customers. How extensive is this impact? 30% of online customers are interrupted to catch one fraudulent attempt One in 10 new applicants may be an imposter using breached data $40 billion of legitimate customer sales are declined annually Businesses must continue their efforts to protect all parties’ interests if they are to thrive in this new world of rapid technological growth. >> Infographic: Global fraud trends

We are excited to announce that Experian Fraud and Identity Solutions is presenting at FinovateFall 2016! Finovate conferences showcase cutting-edge banking and financial technology in a unique demo-only format. Held twice a year, the conferences bring together the leaders from top financial institutions, fintech companies, investors from around the globe, and fintech media to share and promote the most innovative financial technology solutions. "Experian’s Fraud and Identity Solutions is a leader in customer-centric identity and fraud solutions, providing fraud management solutions to some of the world’s largest brands in financial services, insurance, and retail," said Adam Fingersh, general manager and senior vice president of Fraud and Identity Solutions in North America. "We will introduce our Fraud and Identity Solutions and promote our newly released CrossCore platform. CrossCore puts more control in the hands of fraud teams to adapt and deploy strategies that keep up with the pace of fraud while reducing burdens on IT and data science teams." Fingersh and John Sarreal, senior director of Fraud and Identity product management at Experian, are presenting the 7-minute demo focusing on the key CrossCore capabilities, and how CrossCore manages fraud and identity services through its flexible API; open, plug-and-play platform; and powerful workflow and strategy design capabilities. In Forrester’s 2016 “Vendor Landscape: Mobile Fraud Management”, Experian Fraud and Identity Solutions was cited as having the most capabilities and one of the highest estimated revenues in total fraud management in the market, between $200 million and $250 million. Join us for the event on September 8-9 in New York. Experian also has an exclusive 20% off discount code (Experian20FF16) to get even more savings! For more information on the event or to view videos of previous demos, please visit finovate.com.

New industry report highlights the convergence of business growth and fraud prevention strategies Experian has published its first annual global fraud report covering the convergence of growth strategies and fraud prevention. The report, Global Business Trends: Protecting Growth Ambitions Against Rising Fraud Threats, is designed as a guide for senior executives and fraud prevention professionals, offering new insights on how the alignment of strategies for business growth and fraud prevention can help a business grow revenues while managing risks in an increasingly virtual world. The report identifies five trends that businesses should assess and take action on to mitigate fraud and improve the customer experience in today's fast-paced, consumer-centric environment: Applying right-sized fraud solutions to reduce unnecessary customer disruption: It's time to move on from a one-size-fits-all approach that creates more customer friction than necessary. Instead, companies should apply fraud solutions that reflect the value and level of confidence needed for each transaction. This means right-sizing your fraud solutions to align with true fraud rates and commercial strategy. Having a universal view of the consumer is the core of modern fraud mitigation and marketing: Achieving a universal profile of consumer behavior — beyond the traditional 360-degree view — requires access to a combination of identity data, device intelligence, online behavior, biometrics, historical transactions and more, for consumer interactions not only with you, but across other businesses and industries as well. Companies that translate this knowledge and use it to identify consumers can distinguish a fraudster from a real customer more easily, building trust along the way. Expanding your view through a blended ecosystem: In addition to using your own first-party data sources, companies need to participate in a blended ecosystem, working across businesses and even industries. Fraudsters have access to more data than ever before, including data traditionally used to verify identities, and they use that data to create an entire digital profile. Therefore, you can no longer get to the digital interaction data you need by managing the process in a siloed manner. Achieving an expansive view of the universal consumer requires multiple data sources working together. Achieving agility and scale using service-based models: Today, more and more companies are choosing subscription-based systems rather than building in-house or implementing on-premise solutions. Continuous upgrades and the access to new risk logic that come with subscription models provide more agility and faster response to emerging threats, no matter how fast your volume grows or what products, channels or geographies you pursue. Future-proofing fraud solution choices: Companies need access to a wide variety of traditional and emerging technologies and information sources to fill in knowledge gaps and blind spots where fraudsters try to hide. The ability to modify strategies quickly and catch fraud faster while improving the customer experience is a critical aspect of fraud prevention moving forward. Bringing together these key trends, the report provides business leaders with the insight they need to fight fraud using the same consumer-focused approach currently being used to attract new customers and grow revenue. "There is a persistent mindset that fraud loss is just the cost of doing business," said Steve Platt, global EVP, Fraud and Identity, Experian. "But as fraudsters evolve, those losses are climbing, and the status quo is no longer effective or acceptable. We all need to be as forward-looking in fighting fraud as we are in business operations and marketing, and a real understanding of consumers is critical for success. We're talking about the convergence of business growth and fraud prevention, and we're pleased to provide the first report in the marketplace covering this topic." Download the full report here. The report also features an interactive Fraud Prevention Benchmark tool that companies can use to explore how these trends impact their business and how the performance of their approach measures up against industry practices. The report is relevant to functions spanning the enterprise, including C-suite executives such as chief marketing officers (CMOs), chief risk officers (CROs) and chief data officers (CDOs). The report focuses on business processes where fraud infiltrates, including new account opening, account access, money movement transactions, and emerging trends combating fraud, such as advanced fraud analytics. In each area, the report details how multiple business functions can apply responses to create business growth. Steve Platt added: "We hear from our clients that they are most successful when CMOs along with CDOs and CROs all work together to understand the customer and develop fraud management solutions that create a better overall experience." Experian was recently cited in Forrester's 2016 Vendor Landscape: Mobile Fraud Management Solutions1 report and listed as having nine out of a possible 10 capabilities needed to combat mobile fraud. Experian was also identified as one of three leading players in the fraud detection and prevention space in a new study from Juniper Research.2 Experian applied best practices to create a global report on providing fraud management solutions that allow companies to maximize profitability while providing secure, hassle-free customer interactions. Learn more about Experian’s Fraud and Identity business. 1Vendor Landscape: Mobile Fraud Management Solutions, Forrester Research, Inc., June 2016. 2Online Payment Fraud: Key Vertical Strategies & Management 2016–2020, Juniper Research, June 2016.
Many fraud and compliance teams are struggling to keep pace with new business dynamics. Here are several of the many mobile device trends affecting business today: 35% year-over-year growth in mobile commerce from 2014-2015 Value of mobile payment transactions is forecasted to reach more than $27 billion in 2016 45% of smartphone owners use a mobile device to make a purchase every month This rapid growth only reinforces the need for aggressive fraud prevention strategies and the adoption of new technologies to prepare for the latest emerging cybersecurity threats. >> Forrester's 2016 Vendor Landscape: Mobile Fraud Management Solutions Report

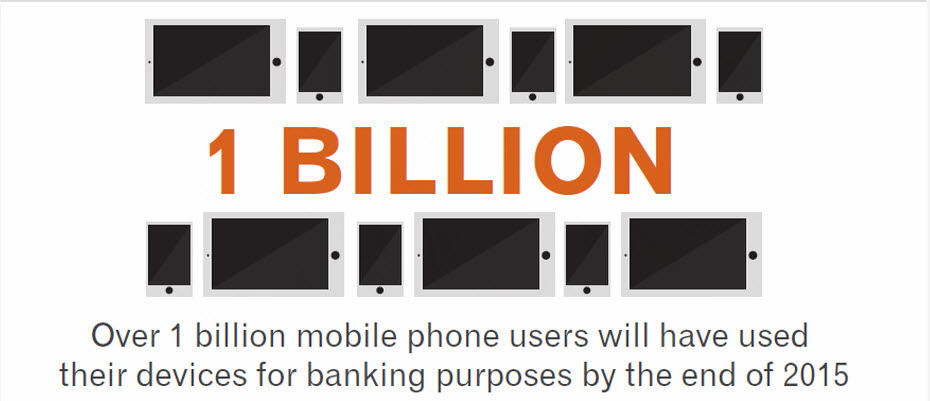
Is the speed of fraud threatening your business? Like many other fraud and compliance teams, your teams may be struggling to keep up with new business dynamics. The following trends are changing the way consumers do business with you: 35 percent year-over-year growth in mobile commerce More than $27 billion forecasted value of mobile payment transactions in 2016 45 percent of smartphone owners using a mobile device to make a purchase every month More than 1 billion mobile phone owners will use their devices for banking purposes by the end of 2015 In an attempt to stay ahead of fraud, systems have become more complex, more expensive and even more difficult to manage, leading to more friction for your customers. How extensive is this impact? 30 percent of online customers are interrupted to catch one fraudulent attempt One in 10 new applicants may be an imposter using breached data $40 billion of legitimate customer sales are declined annually because of tight rules, processes, etc. This rapid growth only reinforces the need for aggressive fraud prevention strategies and adoption of new technologies to prepare for the latest emerging cybersecurity threats. Businesses must continue their efforts to protect all parties’ interests. Fraudsters have what they need to be flexible and quick. So why shouldn’t businesses? Introducing CrossCore™, the first smart plug-and-play platform for fraud and identity services. CrossCore uses a single access point to integrate technology from different providers to address different dangers. When all your fraud and identity solutions work together through a single application program interface, you reduce friction and false positives — meaning more growth for your business. View our recent infographic on global fraud trends

Every day, millions of new things get connected online, such as toasters, heart monitors and cars. Many of these things have weak security controls that create vulnerabilities in critical private networks. As more products get connected, the casual mindset about the security risks inherent in the Internet of Things must begin to change. Here are 12 tips to help safeguard your systems from the Internet of Things. >> Securing the Internet of Things

Experian cited in Mobile Fraud Management Solutions report from Forrester as having the most capabilities and one of the highest estimated revenues in total fraud management